The RFI shall search for feedback regarding how privateness impact assessments might be simpler at mitigating privateness hazards, which includes the ones that are further exacerbated by AI; and
you could possibly currently understand that Google Cloud supplies encryption for data when it truly is in transit or at rest by default, but did you also know we also assist you to encrypt data in use—though it’s remaining processed?
This is recognized as multi-component authentication (MFA) and will involve one smaller more step, for instance a verification code staying sent to an e mail tackle or maybe a telephone. This smaller step can be quite a large leap toward enhanced data stability.
As AI results in being a lot more capable, it has the prospective to electrical power scientific breakthroughs, greatly enhance worldwide prosperity, and safeguard us from disasters. But provided that it’s deployed wisely.
(g) that can help practice the Federal workforce on AI issues, The top of each company shall implement — or improve The provision and use of — AI schooling and familiarization plans for workers, supervisors, and Management in technology along with related plan, managerial, procurement, regulatory, moral, governance, and legal fields. these schooling applications must, for instance, empower Federal staff, professionals, and leaders to create and maintain an working expertise in rising AI systems click here to evaluate possibilities to utilize these systems to reinforce the shipping of services to the general public, and to mitigate hazards linked to these systems.
simply click the button under and take a look at NSYS Data Erasure for your business! Securely erase individual data of former homeowners from utilised telephones with
To fight this hazard, the Federal federal government will be sure that the collection, use, and retention of data is lawful, is secure, and mitigates privateness and confidentiality challenges. companies shall use readily available plan and specialized instruments, which include privacy-improving technologies (Animals) exactly where proper, to protect privacy and also to overcome the broader authorized and societal pitfalls — including the chilling of First Amendment legal rights — that end result in the inappropriate assortment and use of folks’s data.
(i) in 270 times on the day of this buy, establish a approach for world wide engagement on advertising and marketing and building AI criteria, with strains of effort and hard work that could involve:
Plus, there are numerous ways to acquire all-around effectiveness challenges, like the selective encryption of database fields, rows and columns as opposed to encrypting all data in spite of sensitivity.
With this electronic age, the communication landscape has undergone a seismic shift with the advent of digital technologies. From how we interact socially to how corporations function; electronic platforms have remodeled the traditional paradigms of interaction. just about every marketplace is driving communications through channels for example phone calls, chatbots, e mail or messages both speaking with their wellness service provider or money advisors.
Except if your Firm has not long ago performed a data security possibility evaluation, the threat of a data breach is probably much bigger plus much more speedy than you recognize.
10.one. Providing Guidance for AI Management. (a) To coordinate the use of AI over the Federal authorities, in sixty days of your date of this get and on an ongoing foundation as needed, the Director of OMB shall convene and chair an interagency council to coordinate the event and usage of AI in organizations’ applications and operations, besides using AI in nationwide stability programs. The Director of OSTP shall serve as Vice Chair for that interagency council.
(iv) share facts and greatest methods with AI developers and legislation enforcement personnel to establish incidents, advise stakeholders of present-day lawful needs, and Consider AI techniques for IP law violations, and also develop mitigation methods and resources; and
“This study underscores our dedication to acquiring specialised, AI-driven answers for diverse cybersecurity challenges, demonstrating the prospective of AI to revolutionize vulnerability identification and remediation in software devices,” Chen said.
 Jenna Jameson Then & Now!
Jenna Jameson Then & Now! Kenan Thompson Then & Now!
Kenan Thompson Then & Now! Mike Vitar Then & Now!
Mike Vitar Then & Now! Marcus Jordan Then & Now!
Marcus Jordan Then & Now!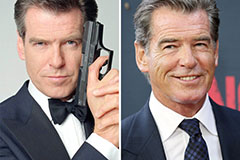 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now!